YOUR DATA IS NUDE! MacOS Install Crash Leaves You Vulnerable – Immediate Danger!
Have you ever encountered a terrifying pop-up on your Mac that screams "The system is in danger" or displays a fake Apple security alert? These alarming messages can make even the most tech-savvy users panic, but what if I told you that these warnings are often elaborate scams designed to steal your personal information and money? In today's digital age, where cyber threats are becoming increasingly sophisticated, understanding how to protect your Mac from these deceptive tactics is more crucial than ever.
The macOS ecosystem has long been touted as more secure than its Windows counterpart, but this reputation has led to a dangerous misconception: that Macs are immune to viruses and malware. While it's true that only about 7% of all malware targets Mac computers compared to 91% for Windows devices, this statistic doesn't mean Macs are invulnerable. Cybercriminals are well aware of the "Mac security myth" and are actively exploiting it through increasingly convincing scams and social engineering tactics.
Understanding the macOS Security Center Scam
The macOS Security Center scam preys on fears of malware and system vulnerabilities, presenting users with alarming messages that appear to come from legitimate Apple sources. These scams typically manifest as pop-ups or browser windows that claim your system is infected or at risk, often using urgent language to create a sense of immediate danger. The goal is to manipulate users into taking hasty actions that benefit the scammers.
- Camila Arujo Leaks
- Pablo Escobar Last Days
- How Many Eggs Does A Chicken Lay A Day The Complete Guide To Egg Production
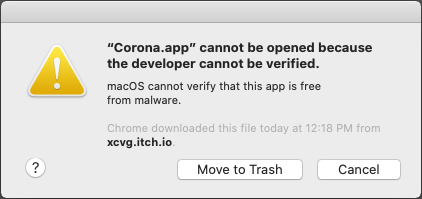
These fraudulent alerts often display official-looking logos, use Apple's signature design language, and even mimic the style of legitimate macOS notifications. They might claim to have detected multiple threats, warn about compromised personal data, or suggest that your system's security has been breached. The sophistication of these scams has increased dramatically, making them difficult for the average user to distinguish from genuine security warnings.
How the Scam Works
To remove the claimed infection, you are given two options: call the listed support number for virus removal assistance, or download a "security tool" to fix the problems. Both options lead to the same destination – financial loss and potential identity theft. When you call the provided number, you'll typically speak with someone claiming to be an Apple support technician who will attempt to convince you to pay for unnecessary services or software.
The second option – downloading the suggested "security tool" – is equally dangerous. These programs are often malware in disguise, designed to steal your personal information, track your online activities, or even encrypt your files for ransom. Some scams may install legitimate-looking but actually malicious software that continues to cause problems long after the initial interaction.
- September 22 Zodiac Sign The Final Day Of Virgo
- Shocking Leak Exposes Madeas Big Happy Family Casts Secret Sex Scandal
- Brian Deegan Net Worth 2024
Step-by-Step Removal Guide
Here's how to get rid of fake Apple security alerts step by step. First, don't panic – these messages, while alarming, are almost certainly scams. Avoid clicking any buttons or calling any numbers displayed in the alert. Instead, force quit your browser by pressing Command + Option + Esc, selecting your browser from the list, and clicking "Force Quit."
Next, clear your browser's cache and cookies, as these scams often rely on malicious scripts that can persist even after you've closed the initial window. If the problem persists, restart your Mac in Safe Mode by holding down the Shift key while booting up. This will prevent third-party software from loading automatically, making it easier to identify and remove malicious programs.
The Truth About Mac Security
But while these messages may look real, they're almost certainly scams. Macs can indeed get viruses, but the ecosystem is designed with multiple layers of security that make infections less common than on other platforms. The macOS includes built-in protections like Gatekeeper, which prevents unauthorized software from running, and XProtect, Apple's built-in antivirus technology.
However, no system is completely immune to threats. Phishing attacks, social engineering, and user error remain the primary ways Mac users fall victim to cybercrime. The key is to remain vigilant and skeptical of any unsolicited security warnings, especially those that create a sense of urgency or demand immediate action.
Dealing with Persistent Pop-ups
The system is in danger fake alert scam by removing adware, and securing your browser. If you've encountered these scams before, you know how frustrating it can be when they keep reappearing. I have run Malwarebytes but it's still popping up – this is a common complaint among Mac users who have dealt with persistent adware and malware.
Adware is particularly troublesome because it often installs itself through bundled software downloads or deceptive installation prompts. Once installed, it can generate constant pop-ups, redirect your web browser to malicious sites, and even track your online behavior. Removing adware requires a multi-faceted approach that includes uninstalling suspicious applications, removing malicious browser extensions, and clearing system caches.
Using Malwarebytes for Mac
Scan with Malwarebytes for Mac to detect and remove malicious software. Malwarebytes searches for malware (short for malicious software) and spyware that can make your Mac act in a misleading manner. This powerful tool can identify threats that traditional antivirus software might miss, including adware, potentially unwanted programs (PUPs), and more sophisticated malware.
To use Malwarebytes effectively, download it directly from the official Malwarebytes website rather than through third-party sources. Run a full system scan and allow the software to quarantine or remove any threats it detects. After the initial scan, consider running regular scans to maintain your system's security, as new threats emerge constantly.
The Consequences of Falling for Scams
To summarize, by trusting the macOS alert scam, users can experience system infections, serious privacy issues, financial loss, and even identity theft. These consequences extend far beyond the initial monetary loss from paying for fake services. Scammers may gain access to your personal information, banking details, and other sensitive data that can be used for identity theft or sold on the dark web.
The financial impact can be substantial, with victims often reporting losses of hundreds or even thousands of dollars. Beyond the direct financial loss, victims may face long-term consequences including damaged credit, fraudulent accounts opened in their name, and the ongoing stress of dealing with identity theft recovery.
Understanding Potentially Unwanted Applications
Scams like macOS alert typically promote various PUPs (potentially unwanted applications). These applications often seem legitimate and harmless and might even be disguised as genuine existing products. PUPs can range from browser toolbars and search hijackers to more sophisticated applications that monitor your activity or display intrusive advertisements.
The danger with PUPs lies in their ability to operate under the radar while collecting data about your browsing habits, search history, and even keystrokes. Some PUPs can modify your browser settings without permission, change your homepage, or redirect your searches to advertising or phishing sites. While not always malicious in the traditional sense, PUPs can significantly degrade your system's performance and compromise your privacy.
Python Security Tools
🚀 Extremely fast fuzzy matcher & spelling checker in Python represents the kind of legitimate security tools that can help protect your system. While this specific tool focuses on text processing and error detection, it demonstrates the importance of using specialized software for different security needs. Python's versatility makes it an excellent platform for developing security tools that can scan for vulnerabilities, detect patterns in malicious code, or automate security testing.
When selecting security tools for your Mac, look for applications that have been vetted by the security community and come from reputable sources. Open-source tools can be particularly valuable because their code is available for public scrutiny, making it easier to verify their legitimacy and effectiveness.
Community Response to Security Threats
The NAE urges the cancellation of the burning represents how security communities respond to emerging threats. Just as fire safety organizations might campaign against dangerous practices, cybersecurity communities work to educate users about emerging threats and promote safe computing practices. This collaborative approach is essential in the fight against cybercrime, as threats evolve rapidly and require coordinated responses.
Security communities share information about new scams, develop tools to combat emerging threats, and provide support to victims of cybercrime. By participating in these communities or following their guidance, users can stay informed about the latest threats and learn effective strategies for protecting their systems.
Password Security Best Practices
Consider using a password manager to generate and store complex passwords. Strong password practices are fundamental to overall system security, yet many users still rely on weak, easily guessable passwords or reuse the same password across multiple sites. A password manager can generate unique, complex passwords for each of your accounts and store them securely, eliminating the need to remember multiple passwords while significantly enhancing your security.
When selecting a password manager, choose one with strong encryption, two-factor authentication support, and a good reputation in the security community. Many password managers also offer additional features like secure note storage, credit card information management, and even VPN services, making them valuable tools for comprehensive digital security.
Data Backup Strategies
Regularly back up your data to protect against data loss from system crashes, malware, or other security incidents. Back up your data regularly to protect against data loss from system crashes, malware, or other security incidents. A comprehensive backup strategy should include multiple backup methods and locations to ensure your data remains safe even if one backup method fails.
Consider using a combination of local backups (external hard drives or network-attached storage) and cloud-based backup services. The 3-2-1 backup rule – three copies of your data, on two different media, with one copy offsite – provides excellent protection against various failure scenarios. Automate your backup processes to ensure consistency and reduce the risk of human error.
The Risks of Outdated Operating Systems
In conclusion, using outdated operating systems can be a significant risk to your system security and performance. When Apple releases new versions of macOS, they often include critical security updates that patch vulnerabilities discovered since the previous release. Running outdated software leaves your system exposed to known exploits that have been patched in newer versions.
Beyond security concerns, outdated operating systems may not receive support for newer applications, hardware, or features. This can lead to compatibility issues, reduced performance, and an inability to use the latest security tools effectively. Always keep your macOS updated to the latest supported version to ensure optimal security and functionality.
Understanding Anarchism and Authority
Anarchism is a political philosophy and movement that is skeptical of authority and rejects all involuntary, coercive forms of hierarchy. Anarchism calls for the abolition of the state, which it holds to be unnecessary, undesirable, and harmful. While this political philosophy may seem unrelated to computer security at first glance, it actually provides an interesting framework for understanding decentralized approaches to security.
The anarchist rejection of centralized authority parallels the cybersecurity principle of distributed defense, where security is maintained through multiple layers and redundant systems rather than relying on a single controlling authority. This approach to security emphasizes user empowerment, transparency, and the distribution of knowledge – all principles that align well with effective cybersecurity practices.
Spectre v2 and CPU Vulnerabilities
Spectre v2 mitigation leaves CPU vulnerable to Retbleed attacks, data leaks possible. This technical detail highlights the complex nature of modern security vulnerabilities, where fixing one issue can sometimes create new attack vectors. The Spectre and Meltdown vulnerabilities, discovered in 2018, affected nearly all modern processors and demonstrated how fundamental hardware design choices could have profound security implications.
These vulnerabilities work by exploiting speculative execution, a performance feature in modern CPUs that predicts which instructions might be needed next and executes them in advance. While this improves performance, it can also leak sensitive information through side-channel attacks. The ongoing research into CPU vulnerabilities demonstrates that security is an evolving field where new threats emerge as our understanding of existing systems deepens.
Ubuntu Security Considerations
Is it a direct bug about security of Ubuntu itself? This question highlights the importance of understanding the specific security implications of different operating systems and software distributions. Ubuntu, like other Linux distributions, has its own security model and vulnerability landscape that differs from macOS and Windows.
Ubuntu's security approach emphasizes user permissions, package management security, and community-driven vulnerability disclosure and patching. The operating system includes AppArmor for application confinement, automatic security updates, and a robust package verification system. Understanding these differences is crucial for users who work with multiple operating systems or are considering switching platforms.
Damn Vulnerable Web Application (DVWA)
License this file is part of Damn Vulnerable Web Application (DVWA). Damn Vulnerable Web Application (DVWA) is free software. You can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation, either version 3 of the license, or (at your option) any later version.
DVWA is an intentionally vulnerable web application designed for educational purposes, allowing users to learn about common web vulnerabilities in a safe, controlled environment. This type of tool is invaluable for security professionals and students who want to understand how attacks work and how to defend against them. By studying vulnerabilities in a safe context, users can develop the skills needed to identify and mitigate similar issues in production systems.
Conclusion
Protecting your Mac from security threats requires a multi-layered approach that combines technical solutions, user education, and ongoing vigilance. The sophisticated scams targeting Mac users demonstrate that no platform is immune to cyber threats, and the consequences of falling victim to these attacks can be severe. By understanding how these scams work, using appropriate security tools, maintaining good security practices, and staying informed about emerging threats, you can significantly reduce your risk of becoming a victim.
Remember that effective security is an ongoing process rather than a one-time setup. Regularly update your software, back up your data, use strong passwords, and remain skeptical of unsolicited security warnings. The digital landscape continues to evolve, and staying safe requires continuous learning and adaptation. By taking a proactive approach to security and understanding the tactics used by cybercriminals, you can enjoy the benefits of your Mac while keeping your data and personal information safe from harm.