The ONE Samsung Tablet IMEI Code Hack They DON'T Want You To Know!
Have you ever wondered if someone could hack your Samsung tablet just by knowing your IMEI number? This question has sparked countless debates and fueled conspiracy theories across the internet. Today, we're diving deep into the world of IMEI security to uncover the truth about what's possible, what's not, and most importantly, how you can protect yourself from real threats.
Understanding IMEI: The Digital Fingerprint of Your Device
IMEI (International Mobile Equipment Identity) is a unique 15-digit code that serves as your device's digital fingerprint. This number identifies your specific smartphone or tablet to mobile networks and carriers worldwide. Think of it as your device's social security number - it holds information about the manufacturer, model, and unique identifier that distinguishes your device from billions of others.
IMEI is embedded in your device's hardware and cannot be changed without physically accessing the device's internal components. This hardware-level integration makes IMEI fundamentally different from software-based identifiers that can be modified or spoofed through applications.
- James May Wife
- You Wont Believe These Leaked Fort Lauderdale Activities From Nude Cruises To Secret Parties
- Movierulzvpn
The Dark World of IMEI Hacking: Separating Fact from Fiction
Let's address the elephant in the room: can someone actually hack your device using just your IMEI number? The short answer is no, but the complete answer requires understanding what IMEI can and cannot do.
Without physical access to your phone or its operating system, the IMEI remains a passive identifier that cannot be used to hack a phone. Claims that a phone can be hacked solely through its IMEI are misleading and unfounded. The IMEI number alone doesn't provide any pathway to control, access, or manipulate your device remotely.
However, this doesn't mean your IMEI is completely harmless if exposed. While you can't be hacked through your IMEI, there are other risks associated with its exposure that every device owner should understand.
- Sinbad Legend Of The Seven Seas A Dreamworks Animated Classic
- Shocking Sex Scandal At Moxy Lower East Side Leaked Photos Go Viral
- After Sex How Long Can Your Period Be Late The Dangerous Truth Exposed
IMEI Cloning vs. Hacking: Understanding the Real Threat
Many people confuse IMEI hacking with IMEI cloning and SIM swapping. IMEI cloning involves replicating a legitimate device's IMEI number onto another device. This practice is illegal in most countries and is typically used for fraudulent activities like making international calls on someone else's account or bypassing carrier restrictions.
SIM swapping, while related to device identity, is a separate attack vector that involves social engineering to convince your carrier to transfer your phone number to a different SIM card. This allows attackers to intercept calls, messages, and potentially bypass two-factor authentication.
These are the real threats in the mobile security landscape, not direct IMEI hacking. Understanding this distinction is crucial for protecting yourself effectively.
What Can Someone Actually Do With Your IMEI Number?
If a malicious actor gets hold of your IMEI number, they can report your device as stolen to your network carrier. As a result, your phone could be blocked from accessing cellular services, rendering it useless. This is particularly concerning if you're traveling internationally or rely on your device for business communications.
Network carriers use IMEI blacklists to block stolen devices from their networks. If someone maliciously reports your device as stolen, you might find yourself unable to use cellular data, make calls, or send texts, even though your device is perfectly fine.
Additionally, IMEI numbers can be used to identify your device's make, model, and specifications. While this information alone isn't particularly dangerous, it can be combined with other data points in identity theft schemes or targeted phishing attacks.
The Truth About IMEI Protection Measures
Mobile network operators and device manufacturers have implemented several measures to deter and track any attempts at changing IMEI numbers. These include:
- IMEI blacklisting databases that share information across carriers globally
- Hardware-level security features that make IMEI modification extremely difficult
- Legal frameworks in many countries that criminalize IMEI tampering
- Advanced tracking systems that can detect suspicious IMEI changes
These measures make large-scale IMEI fraud significantly more challenging for cybercriminals, though determined attackers may still find ways to exploit vulnerabilities in specific situations.
Protecting Your Mobile Security: Essential Strategies
Now that we understand what's real and what's not regarding IMEI security, let's focus on essential protection strategies to safeguard your mobile security:
Never share your IMEI number publicly or with untrusted parties. Just like you wouldn't share your social security number with strangers, treat your IMEI with similar caution. Only provide it to authorized service centers, your carrier when necessary, or in situations where you're certain of the recipient's legitimacy.
Use strong passwords and biometric authentication on your device. While your IMEI can't be used to hack your device directly, weak authentication methods make it easier for physical thieves to access your data if they obtain your device.
Keep your device's operating system and applications updated. Security patches often address vulnerabilities that could be exploited if someone gains physical access to your device.
Be cautious of phishing attempts that might try to trick you into revealing your IMEI or other personal information. Legitimate companies will rarely ask for your IMEI number unsolicited.
What To Do If Your IMEI Is Compromised
If you suspect your IMEI number has been compromised or misused, take immediate action:
Contact your mobile carrier immediately to verify whether any suspicious activity has been detected on your account. They can check if your device has been reported as stolen or if there are any unusual patterns in your account activity.
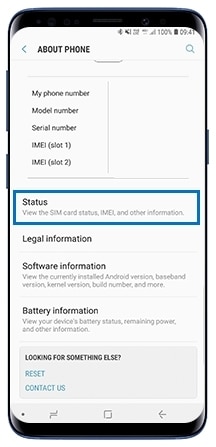
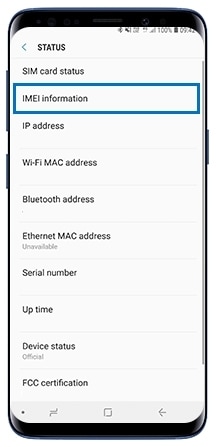
Document your IMEI number and keep it in a secure location. You can find it in your device settings, on the original packaging, or by dialing *#06# on most phones. Having this information readily available helps you respond quickly if issues arise.
Consider using device tracking services like Samsung's SmartThings Find or similar services from other manufacturers. These services allow you to remotely locate, lock, or erase your device if it's lost or stolen, providing an additional layer of security beyond IMEI protection.
The Role of Device Tracking in Modern Security
Losing your Galaxy phone or tablet can be stressful and upsetting. Luckily, your Galaxy device comes with SmartThings Find and Samsung Find, which lets you remotely locate or lock your device if the need ever arises. You can also erase your device's data, so no one will have access to your information.
These tracking services use a combination of GPS, Wi-Fi, and cellular data to pinpoint your device's location. They also offer features like:
- Remote locking to prevent unauthorized access
- Data erasure to protect your personal information
- Offline finding using nearby Galaxy devices to locate your lost device
- Battery status monitoring to help you recover your device before it powers off
Recovering Access to Your Device
If you've forgotten your password or PIN, most modern devices offer recovery options. For Samsung tablets, you can use Android Device Manager or your Google account to reset access. The process typically involves:
Verifying your identity through secondary authentication methods
Resetting your device password through official recovery channels
Restoring from backup once you regain access to ensure you don't lose important data
These recovery methods are designed to be secure while still providing access when you're locked out legitimately.
Understanding the Real Risks of IMEI Exposure
Let's explore the risks associated with exposing your IMEI number and offer tips on how to protect your personal information. While IMEI exposure isn't as catastrophic as some fear, it's still worth understanding the potential consequences:
Network blocking is the most immediate risk if someone maliciously reports your device as stolen. This can leave you without cellular service until you resolve the issue with your carrier.
Device identification allows others to know your device's make, model, and potentially its age. This information could be used in targeted attacks or to determine the value of your device for theft purposes.
Fraudulent warranty claims could theoretically be made using your IMEI, though this is relatively uncommon and typically caught by manufacturer verification processes.
The Future of Device Security
As mobile technology continues to evolve, so do the methods used to protect and potentially exploit device identifiers like IMEI. Manufacturers are increasingly implementing hardware-based security features that make traditional forms of device identity theft more difficult.
Biometric authentication, hardware security modules, and advanced encryption are becoming standard features that complement traditional IMEI-based identification. These technologies work together to create multiple layers of security that protect your device and data.
Conclusion: Knowledge Is Your Best Protection
The world of mobile security can seem overwhelming, especially with so much misinformation circulating about what's possible and what's not. The truth about IMEI hacking is that while your device cannot be directly hacked through its IMEI number alone, there are still legitimate concerns about IMEI exposure and misuse.
Understanding the difference between what's possible and what's not is your best defense against mobile security threats. By knowing that IMEI cloning and SIM swapping are the real risks rather than direct IMEI hacking, you can focus your protective efforts where they matter most.
Remember to keep your device secure with strong authentication, keep your software updated, be cautious about sharing your IMEI number, and use the built-in security features provided by your device manufacturer. With these practices in place, you can enjoy the benefits of mobile technology while minimizing the risks.
The next time someone asks "can someone hack your phone by IMEI number," you'll have the knowledge to provide an accurate, informed answer and guide them toward real security practices that actually protect their digital life.