EXPOSED: The Dark Truth About MVP Win555 CFD's Leaked Secrets!
Have you ever wondered what happens when sensitive information falls into the wrong hands? In today's digital landscape, the consequences can be devastating—from corporate espionage to personal identity theft. The case of MVP Win555 CFD serves as a chilling reminder of how exposed secrets can compromise everything we hold dear. But what if you could stop breaches before they happen? What if you could monitor compromised credentials, exposed infrastructure, and sensitive data leaks across the surface, deep, and dark web before attackers can exploit them?
The Hidden Dangers of Exposed Information
In our interconnected world, information leaks have become alarmingly common. Whether it's a corporate database breach or personal data exposure, the ripple effects can be catastrophic. The MVP Win555 CFD incident reveals just how vulnerable organizations and individuals truly are in the digital age.
When secrets are exposed, the damage extends far beyond the initial breach. Financial losses, reputational damage, and legal consequences can follow. The question isn't whether you'll be targeted—it's when. And by then, it's often too late to prevent the fallout.
- Exposed The Barrel Roll X200 Challenge That Broke The Internet And Left Fans In Tears
- Backstreet Boys Age When They Started
- Hot Summer Nights Cast Exposed Leaked Nude Photos Shock Fans
Monitoring the Digital Underground
The Three Layers of the Web
The internet exists in three distinct layers: the surface web (what we use daily), the deep web (password-protected and private content), and the dark web (anonymous networks where illicit activities thrive). Each layer presents unique monitoring challenges, but all require vigilance.
Security researchers like Bill Demirkapi have demonstrated the scale of the problem. In his investigations, he found more than 15,000 hardcoded secrets and 66,000 vulnerable websites—all by searching overlooked data sources. These numbers represent real-world vulnerabilities that could be exploited at any moment.
Proactive Threat Intelligence
The key to preventing breaches lies in proactive monitoring. By scanning the dark web, deep web, and surface web continuously, organizations can identify compromised credentials and exposed infrastructure before attackers do. This approach transforms cybersecurity from a reactive to a proactive discipline.
- Age Of The Backstreet Boys
- Susan Egans Secret Porn Past Revealed In Leaked Tapes Hollywood In Outrage
- Gypsy Rose Crime Sean
Tools and services that specialize in dark web monitoring can alert you when your information appears in places it shouldn't. Whether it's a leaked password, exposed API key, or sensitive document, early detection provides the critical window needed to mitigate damage.
Corporate Security: A Single Point of Failure
The Employee Factor
When it comes to corporate security, a leaked password from at least one employee can have tragic consequences for the entire company. This single point of failure can cascade through an organization's entire digital infrastructure, compromising customer data, intellectual property, and financial information.
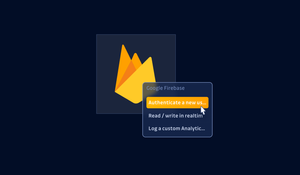
GitHub, being a widely popular platform for public code repositories, may inadvertently host such leaked secrets. Developers often accidentally commit sensitive information to public repositories, creating vulnerabilities that persist long after the initial mistake.
Comprehensive Secret Scanning
To help identify these vulnerabilities, I have created a comprehensive search list using powerful search syntax that enables the search of thousands of leaked keys and secrets in a single search. This approach leverages advanced search operators to uncover exposed credentials, API keys, and other sensitive information that might otherwise remain hidden.
The methodology involves scanning for patterns that indicate secrets—API keys, passwords, encryption keys, and other credentials. By using specialized search syntax, security researchers can uncover vulnerabilities that traditional security tools might miss.
The Human Cost of Information Exposure
Stories of Spiritual Abuse and Manipulation
The digital world isn't the only place where secrets can be exposed. Sometimes, the most damaging revelations come from personal experiences. Hear the untold stories of victims who were spiritually abused and manipulated, and see the leaked text messages where leaders admitted Shawn was dangerous but refused to warn the public.
These revelations highlight a disturbing pattern: when those in positions of authority become aware of dangers but fail to act, the consequences can be devastating. The refusal to warn the public about known threats represents a betrayal of trust that extends beyond digital security into the realm of personal safety and well-being.
The Role of Fact-Checking in the Digital Age
In an era of misinformation, the definitive internet reference source for urban legends, folklore, myths, rumors, and misinformation plays a crucial role. Sites dedicated to debunking false claims and verifying information help combat the spread of harmful content that can result from exposed secrets.
The challenge lies in distinguishing between legitimate security concerns and baseless rumors. Fact-checking organizations provide the verification needed to separate genuine threats from fear-mongering, helping individuals and organizations make informed decisions about their security posture.
Personal Data Protection
Have I Been Pwned: A Critical Resource
Have I been pwned allows you to check whether your email address has been exposed in a data breach. This free service, created by security expert Troy Hunt, maintains a database of billions of compromised accounts from thousands of data breaches.
By entering your email address, you can discover if your information has been part of any known data breaches. This knowledge empowers you to take action—changing passwords, enabling two-factor authentication, and monitoring accounts for suspicious activity.
Best Practices for Personal Security
Beyond breach monitoring, individuals should adopt comprehensive security practices. These include using unique passwords for each account, enabling multi-factor authentication wherever possible, and being cautious about sharing personal information online.
Regular security audits of your digital presence can reveal vulnerabilities before they're exploited. This includes checking for exposed information on the dark web, reviewing privacy settings on social media, and ensuring that old accounts are properly deactivated or deleted.
The GitHub Problem
Accidental Exposure of Secrets
GitHub, being a widely popular platform for public code repositories, may inadvertently host such leaked secrets. Developers often commit sensitive information by mistake, including API keys, passwords, and other credentials. These secrets remain accessible until discovered and removed.
The scale of this problem is significant. Research indicates that thousands of secrets are exposed on GitHub daily, creating a vast attack surface for malicious actors to exploit. Automated tools can scan repositories for exposed credentials, but the sheer volume of code makes complete coverage challenging.
Preventive Measures for Developers
Developers must adopt security-conscious practices to prevent secret exposure. This includes using .gitignore files to prevent sensitive files from being committed, employing pre-commit hooks that scan for secrets, and using environment variables instead of hardcoding credentials.
Additionally, organizations should implement secrets management solutions that provide secure storage and rotation of credentials. These tools can integrate with development workflows to ensure that secrets never appear in source code repositories.
The Business Impact of Data Breaches
Financial Consequences
Data breaches carry significant financial costs beyond the immediate theft. Organizations face regulatory fines, legal settlements, and the expense of incident response and remediation. The average cost of a data breach continues to rise, with some incidents costing millions of dollars.
Reputational damage often proves even more costly than direct financial losses. Customers lose trust in organizations that fail to protect their data, leading to decreased sales, lost business opportunities, and long-term brand damage that can take years to repair.
Regulatory Compliance
Data protection regulations like GDPR, CCPA, and industry-specific requirements mandate specific security measures and breach notification protocols. Organizations must demonstrate due diligence in protecting sensitive information or face substantial penalties.
Compliance isn't just about avoiding fines—it's about implementing security practices that genuinely protect data. This includes regular security assessments, employee training, incident response planning, and documented security policies.
Conclusion
The dark truth about MVP Win555 CFD's leaked secrets represents just one example of a pervasive problem affecting organizations and individuals worldwide. From corporate espionage to personal data exposure, the consequences of compromised information continue to escalate in our digital age.
The solution lies in proactive monitoring, comprehensive security practices, and a commitment to protecting sensitive information at every level. By understanding the risks, implementing appropriate safeguards, and staying informed about emerging threats, we can reduce our vulnerability to data breaches and their devastating consequences.
Remember: the best time to address security vulnerabilities is before they're exploited. Whether you're an individual concerned about personal data or an organization protecting valuable assets, taking action today can prevent the painful consequences of tomorrow's breaches. The truth about leaked secrets may be dark, but our response to them can shine a light on a more secure future.
.jpg)