NUDES LEAKED! How Your Area Code In New York Is Ruining Lives – Must Read Now!
Have you ever wondered how a single intimate photo could spiral into a nightmare that destroys your reputation, career, and mental health? In New York, victims of sextortion are discovering that their area code might be the very thing that makes them targets. With intimate images being shared without consent at alarming rates, understanding your rights and knowing how to fight back has never been more critical. This comprehensive guide will walk you through everything you need to know about protecting yourself from digital exploitation.
Understanding Your Rights: The Victim Services Division
When your intimate images are leaked online, knowing where to turn for help can feel overwhelming. The Victim Services Division provides crucial support for individuals who have fallen prey to sextortion and revenge porn. These specialized professionals understand the trauma associated with having your private moments exposed to the world and can guide you through the legal and emotional recovery process.
The division offers confidential counseling, legal referrals, and assistance with removing illegal content from websites. They can also help you understand the specific laws in New York that protect victims of non-consensual image sharing. Many victims don't realize they have legal recourse, and the Victim Services Division can explain how New York's revenge porn laws apply to your situation, regardless of your area code or location within the state.
- Coronilla De La Divina Misericordia Exposed The Miracle That Will Blow Your Mind
- You Wont Believe These Leaked Fort Lauderdale Activities From Nude Cruises To Secret Parties
- Exclusive Leaked Video Shows Wild Party At Mount Magazine State Park Porn Scandal
Legal Definitions: What the Law Actually Says
For purposes of New York's revenge porn statutes, understanding the specific legal terminology is essential to building your case. The law defines "intimate part" as the naked genitals, pubic area, anus, or female nipple of a person. This precise definition matters because it determines what types of images are protected under the law. Even partially clothed images that reveal these areas may fall under legal protection.
The terms "disseminate" and "publish" have specific meanings in this context, as defined in section 250.40 of the New York Penal Law. These terms encompass not just posting on social media, but also sending through messaging apps, uploading to file-sharing sites, or any other form of distribution. Understanding these definitions helps victims identify all potential violations and ensures law enforcement can pursue the full extent of legal action available.
Fighting Back: Expert Digital Forensics Support
When intimate images are leaked, the digital trail becomes your strongest weapon. Digital forensics experts specialize in tracking where your images have been shared, identifying the perpetrators, and providing the evidence needed for legal action. These professionals use sophisticated tools to uncover metadata, IP addresses, and other digital footprints that might otherwise remain hidden.
- Emotional Explosion What Your Heart Truly Wishes For In Every Dream
- Whats Dry Begging
- Shocking Video 212 Lab Divide By X Leak This Changes Everything You Know
The process of fighting back begins with immediate action. Digital forensics teams can help you create a comprehensive inventory of where your images have appeared online, which is crucial for takedown requests and potential lawsuits. They can also advise on steps to prevent further distribution and help you understand the scope of the damage. Many victims find that having concrete evidence empowers them to take control of the situation rather than feeling helpless.
The Epstein Files: Understanding the Scope of Digital Exploitation
The database released by the Justice Department, representing the largest release of files to date in the yearslong investigations into Jeffrey Epstein, reveals the vast scale of digital exploitation networks. While Epstein's case involved different criminal activities, the methods of digital manipulation and exploitation share disturbing similarities with modern sextortion cases. The files show how sophisticated networks can operate across multiple jurisdictions, making prosecution challenging.
This massive data release demonstrates why immediate action is crucial when intimate images are leaked. Just as investigators had to piece together years of digital evidence, victims of sextortion need to act quickly to preserve their own digital evidence. The Epstein case also highlights how technology can be used to facilitate exploitation on a massive scale, underscoring the importance of robust digital protection measures.
Global Action: The Need for Immediate Legislative Response
As European negotiators call for new laws to criminalize cyberviolence and cyberporn, the urgency of addressing these issues becomes clear. From a survivor's perspective, waiting for legislative changes while your life is being destroyed online is not an option. The delay in implementing stronger protections allows perpetrators to continue their harmful activities with minimal consequences.
The push for new legislation recognizes that current laws often lag behind technological capabilities. Many existing statutes were written before the rise of social media and instant messaging, leaving significant gaps in protection. Survivors emphasize that immediate action is needed to close these loopholes and provide real protection for victims. This includes not just criminal penalties but also mechanisms for rapid content removal and support services.
Understanding the Psychology of Perpetrators
Why do people engage in sextortion and revenge porn? Understanding the psychology behind these crimes can help victims recognize warning signs and protect themselves. Many perpetrators act out of a desire for power, revenge, or financial gain. Some operate as part of organized crime networks that use sextortion as a lucrative business model, while others are former partners seeking to harm their exes.
The psychological impact on victims is profound and long-lasting. Beyond the immediate embarrassment and violation of privacy, victims often experience anxiety, depression, and post-traumatic stress. The knowledge that intimate images can resurface at any time creates a persistent sense of vulnerability. Understanding these psychological dynamics helps victims recognize that the blame lies entirely with the perpetrator, not themselves.
Prevention Strategies: Protecting Yourself Before It's Too Late
Prevention is always better than cure when it comes to protecting your intimate images. Start by understanding that once an image is digital, you lose control over where it might end up. Consider using secure messaging apps with end-to-end encryption, and be cautious about sharing intimate content even with trusted partners. Remember that relationships can change, and what seems safe today might become ammunition tomorrow.
Technical measures can provide additional protection. Use strong, unique passwords for all accounts, enable two-factor authentication, and be wary of phishing attempts that could compromise your accounts. Consider the metadata in your photos - many images contain GPS coordinates and other identifying information. Before sharing any intimate images, understand the potential long-term consequences and whether the temporary pleasure is worth the permanent risk.
Taking Action: Your Step-by-Step Recovery Plan
When you discover that your intimate images have been leaked, having a clear action plan can make the difference between feeling overwhelmed and taking control. Start by documenting everything - take screenshots of where the images appear, note any threatening messages, and preserve all evidence. Contact local law enforcement and provide them with the documentation you've gathered.
Next, work with a digital forensics expert to identify the extent of the distribution and develop a takedown strategy. Many websites have policies against non-consensual intimate images and will remove them when properly notified. Consider working with an attorney who specializes in revenge porn cases - they can help you understand your legal options, including potential civil lawsuits against perpetrators.
The Role of Social Media Platforms and Tech Companies
Major social media platforms and tech companies have a responsibility to protect users from non-consensual intimate image sharing. Many have implemented reporting systems and content moderation policies specifically designed to address revenge porn and sextortion. However, the effectiveness of these measures varies widely, and many victims report frustration with slow response times or inadequate support.
Advocacy groups are pushing for stronger platform accountability, including mandatory reporting of sextortion attempts and improved content moderation algorithms. Some platforms now offer features that allow users to proactively protect their images by uploading them for fingerprinting, which prevents them from being shared even if someone tries to upload them later. Understanding these tools and how to use them can provide an additional layer of protection.
Building a Support Network: You're Not Alone
One of the most damaging aspects of sextortion is the isolation victims often feel. Many suffer in silence due to shame or fear of judgment. However, building a support network is crucial for recovery. This might include trusted friends and family, support groups for survivors of image-based abuse, and professional counseling services.
Online communities can also provide valuable support, though it's important to engage cautiously and protect your privacy. Many survivors find strength in connecting with others who understand their experience. These connections can provide practical advice, emotional support, and sometimes even lead to collective action for stronger protections and support services.
The Future of Digital Privacy and Protection
As technology continues to evolve, so too must our approaches to protecting intimate privacy. Emerging technologies like blockchain and advanced encryption offer new possibilities for secure image sharing and verification. At the same time, artificial intelligence is being developed to detect and prevent the non-consensual sharing of intimate images before they can cause harm.
The conversation around digital privacy is also expanding to include education and prevention. Schools, universities, and community organizations are beginning to implement comprehensive digital citizenship programs that address the responsible use of technology and the consequences of sharing intimate images. These proactive approaches aim to create a culture where sextortion and revenge porn are universally recognized as unacceptable and where victims receive immediate support rather than judgment.
Conclusion: Taking Back Control
The nightmare of having your intimate images leaked can feel overwhelming, but you have more power than you realize. By understanding your rights, taking immediate action, and building a support network, you can fight back against those who seek to exploit you. The legal landscape is evolving to provide better protections, and technology is developing new tools to prevent and address these violations.
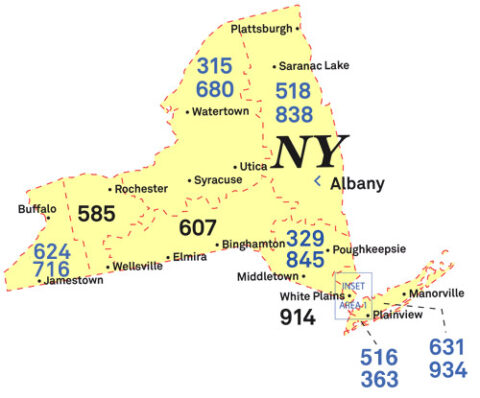
Remember that you are not alone in this fight. Thousands of people in New York and beyond have faced similar situations and have successfully reclaimed their lives and reputations. The key is to act quickly, document everything, and seek help from professionals who understand these complex issues. With the right support and knowledge, you can not only recover from this violation but also help prevent it from happening to others. Your area code doesn't define your worth, and with proper action, you can ensure that one mistake or malicious act doesn't define your future.